2 min read
From the Blog

8 min read
Boost Your Business: A Guide to IT Managed Services for the Small Business Owner
Considering managed IT services for your small business? Access to technology expertise, improved security, and strategic growth support are within...

2 min read
5 Reasons Location Matters When Choosing an MSP
It's tempting to believe that, in this age of connectivity, the location of your managed service provider (MSP) is irrelevant. With remote support...

3 min read
Navigating Growth: Five Signs You’ve Outgrown Your Current Managed Service Provider
As your organization evolves, so do its technological demands. Identifying when your current MSP no longer meets these changing needs is key to...

2 min read
6 Ways IT Mismanagement Stifles Business Growth
In the rapidly evolving landscape of modern business, the role of IT has outgrown the idea that it’s simply a support function. It’s now a driver of...

3 min read
The Integral Role of IT Management in Business Strategy: How Size Matters
Information Technology is often the heartbeat of an organization, fueling its operations and future ambitions. When strategizing the role of IT...

3 min read
Streamlining Employee On-boarding and Off-boarding with an MSP: IT Considerations and Benefits
The on-boarding and off-boarding of employees are integral processes that demand meticulous planning and execution. The Information Technology team...

2 min read
Beyond the Obvious: Unveiling the Hidden Benefits of Managed Service Providers

2 min read
Why Sagiss Doesn't Offer "All You Can Eat" Contracts: Putting Service First
In the dynamic world of IT managed services, finding the perfect balance between service quality, client satisfaction, and business sustainability is...

4 min read
How Sagiss Crafts the Perfect Managed Services Contract to Fit Your Business
At the heart of any successful engagement with an IT managed service provider (MSP) is the contract that details the scope of work. The Statement of...

3 min read
Infrastructure as a Service: A Growing Force in Cloud Computing
Infrastructure as a service (IaaS) offers a flexible, scalable, and cost-efficient solution to simplify the complexity of managing IT infrastructure....

4 min read
MSPs Are Key to Unlocking IT Network Agility for Business
Agile has become a buzzword in business circles for some time now and for good reason. Agile organizations outperform their peers by as much as 50%...

3 min read
Overcoming IT Complexity During Mergers and Acquisitions
When two people get married and buy a house, they have to figure out which furniture to move in, what items to keep, what things to get rid of, and...

3 min read
The Internet of Things (IoT) Creates Benefits, Challenges, and Opportunities for Businesses
The Internet of Things (IoT) is one of the fastest areas of growth in IT. The market for IoT devices was valued at $544 billion in 2022 and is...

4 min read
Break-Fix vs. Managed Service Provider: What Is Right for Your Business?
In the not-too-distant past, when something broke, you’d call in someone to repair it and wait for the repair to happen. That may have been fine when...

3 min read
7 Questions You Should Ask an MSP Before Hiring Them to Migrate You to the Cloud
Cloud migration is more complex than it might seem at first. Companies often find that out the hard way.
3 min read
Need Top IT Talent? Look No Further Than Sagiss
With all the layoffs in the tech sector making news these days, you’d think there might be readily-available talents to fill all the open IT jobs....

5 min read
Talking Tech: Translating Technology for Understanding
Has this ever happened to you? As a business leader, you ask what seems like a simple question, and you get a long-winded answer that uses a lot of...

3 min read
Effective IT Should Be Unnoticed
IT infrastructure is the backbone of nearly every business. Reliability, resiliency and security are key to success and productivity. When the system...

4 min read
What You Get When Working With Sagiss
IT systems today are incredibly complex. We depend on them to run our businesses, but what happens when something breaks down?

6 min read
How to Adopt a Managed Services Mentality
Businesses of all sizes are looking for ways to streamline processes and reduce expenses without sacrificing quality or reliability. Utilizing...

4 min read
Why You Need an MSP That Is Cyber Verified
The managed service provider (MSP) you choose to work with is a significant decision. You need to be able to trust they can provide the services you...

3 min read
The SOC 2 Audit Process and Why it Matters
In the past year, cybercriminals have escalated their attacks on companies. Cyberattacks have reached an all-time high and they have become more...

4 min read
What Is a Virtual CIO and How Can a vCIO Help Your Business Grow?
Business leaders focus on running things smoothly, maximizing profits, and delivering the bottom line. Yet, there are so many things that can be...

4 min read
What Makes Sagiss Different from Other Managed Service Providers (MSPs)
Managing IT is a significant challenge for small and medium-sized companies. Most can’t afford to hire an IT team or Chief Information Officer, staff...

5 min read
Using Multifactor Authentication? Beware of MFA Fatigue and MFA Spamming
Multifactor authentication (MFA) is an effective tool for stopping unauthorized access to networks and websites, even if passwords are compromised....

4 min read
Disaster Recovery as a Service: A Necessity, Not a “Nice-To-Have”
It’s interesting how ancient stories can remain relevant across millennia: despite having made huge strides as a species, humanity continues to...

5 min read
Public Vs Private Cloud
Most of us have taken lessons of some sort — pottery, coding, cello, or public speaking. Let’s say you’re interested in learning more about rock...

1 min read
Think before you click
People often look to sophisticated tools for security solutions.

1 min read
Remote managed IT services - How do they work?
One question we often get concerns the benefits of remote managed IT vs. on-site support.

2 min read
Is a fractional CIO a good fit for your business?
Businesses have an endless list of needs but may not have the resources to satisfy all their needs in-house. That's why many businesses outsource...

1 min read
MSP vs MSSP - What are the differences?
The masses are often confused by the terms "MSP" and "MSSP". They may think there's no difference because the two are differentiated only by an extra...

2 min read
Security is a team effort
In decades past, job responsibilities were reserved for specific departments. One department had one type of people who performed one type of task.

1 min read
Security dos and don'ts
Solid security is, in many ways, complicated. Fortunately, there are a few basics you can follow to tighten up your security right away and get high...

1 min read
What is threatware?
Threatware is not a common term, so you may think it's a new class of cyber threat. But threatware is an umbrella term including many common security...
5 min read
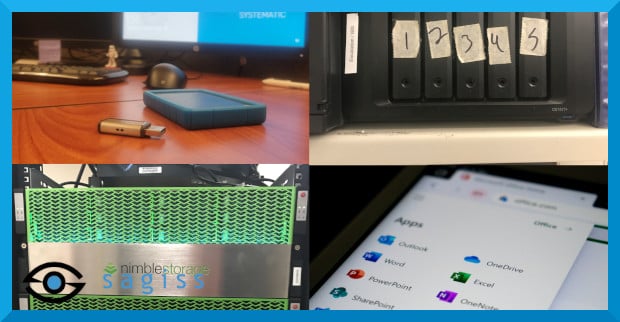
The 4 most common types of data storage
The world runs on data. And businesses now have access to more data than ever before.
1 min read
The benefits of co-managed IT
When most people think of outsourced or managed IT, they likely think of fully-managed IT. With fully-managed IT, you rely on a managed service...

3 min read
Why Microsoft Edge is the best web browser for business
Microsoft Edge recently passed Safari as second place in the desktop browser wars. But Edge should hold the top spot as the web browser for business.

2 min read
How technology fits into business continuity planning
Every business needs a business continuity plan.

2 min read
Microsoft end-of-life survival kit
Nothing good lasts forever. Even Microsoft products.

3 min read
Why internal policies are crucial for managed security success
Once upon a time, good security amounted to little more than protecting your perimeter to keep threat actors out of your networks. But now, with the...

4 min read
What is the cost of a data breach?
Year after year, data breaches are getting more expensive.

2 min read
Pros and cons of BYOD
Businesses are always looking for ways to save money. Rather than buy more devices for their employees, some businesses implement BYOD programs.

2 min read
What is emotet?
Emotet, one of the worst security threats ever created, originated in 2014 as malware that intercepted internet traffic and harvested sensitive...

4 min read
10 security red flags to avoid
Sometimes you hear a piece of advice so harmful that it grates your ears like nails on a chalkboard. You might call such advice "red flags."


